Round 7: Spammer vs. Barracuda…FIGHT!
Just in case you’ve been keeping track, this is the seventh time a Spammer has forged one of the domains under my control as the return address of their Spam run. The first time it happened I felt shocked, angered, and betrayed. After I lost count of the incidents on my left hand and had to move on to my right hand to keep track it now just feels old-hat. Sure, it still pisses me off, but I now just chalk it up to being the owner of many high profile domain names.
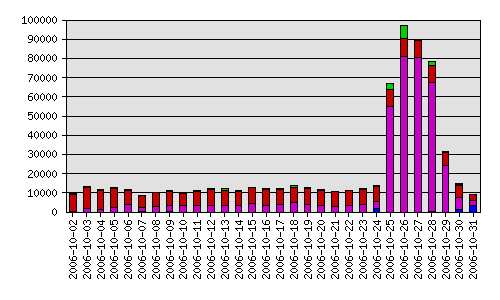
Previously I noticed Spam runs immediately because the mail server started choking on the influx of bounces. This time the domain in question had a Barracuda Spam Firewall 200 sitting on the front lines in the DMZ; I didn’t notice the barrage until the midnight reports ran and I received the pretty pie charts showing a 600% increase in e-mail (and that was just the first day).
Days 2 and 3 jumped up to a 800% to 900% increase in e-mail before starting to plateau and drop off on Day 4. All in all around 350,000 bounces were blocked which is pretty routine for a forged run but the Barracuda performed without so much as a hiccup.
And, for the more visual among you, I’ve of course attached the obligatory pretty graph to show what a Spam forgery looks like. Green is legitimate e-mail, red is blocked Spam, magenta is bad recipient, and blue is rate control (too many connections).
1 thought on “Round 7: Spammer vs. Barracuda…FIGHT!”
Comments are closed.
Although it certainly doesn’t prevent domain hijacking, setting up an SPF record will certainly cut down the amount of it.